| Blog - Comodo One News |
|---|
|
IT Security ProvidersAugust31, 2018

Cyber threats are on the rise globally, and many businesses are extremely vulnerable to it as a result of ineffective IT security strategies. Security solutions provided by IT security providers are essential for all kinds of organizations, particularly when considering the importance of the internet and the IT systems for running the day-to-day operations of an organization. Learn More |
|
CRM Definition, BenefitsAugust28, 2018

Customer Relationship Management (CRM) software refers to the tools, techniques, strategies, and technologies employed by enterprises for developing, acquiring, and retaining customers. This software guarantees that every single step while interacting with consumers goes efficiently and smoothly in order to increase the overall profits. Learn More |
|
Top 10 Best Network Monitoring Tools of 2018 August 17, 2018
Network monitoring provides enterprises with a comprehensive view of their network and current status, and also allows them to identify ways that will help enhance the overall performance of the processes and address different security vulnerabilities. A Network monitoring tool is capable of permitting Managed Service Providers (MSP) to gain an actual picture of the existing network of new customers, prior to signing a service providing contract. Learn More |
|
Customer Relationship ManagementAugust 17, 2018

Customer Relationship Management (CRM) enables a business to cut costs and increase profits. CRM systems are used to organize, automate, and track business processes like lead generation, marketing, forecasting, sales, ROI measurement, and customer service. Hence, the purpose of a CRM system is to boost integration in these areas and also measure and track the value of customer relationships with the ultimate goals of increased profitability and efficiency. Learn More |
|
Best CRM Software of 2018August 21, 2018

You have probably heard of Customer Relationship Management (CRM) — but what exactly does CRM mean and what is the best CRM software? Let's find out! At a high level, CRM software makes life easier for customer support teams. The aim of CRM software is to better customer relationships; CRM software enables businesses to scale up the process of building better relationships with its customers. Learn More |
|
What is Project Management Software?August 08, 2018

Project management software is software that is used for project planning, resource allocation, scheduling, and change management. It permits project managers (PMs), users and stakeholders to control costs and manage budgeting, documentation and quality management. Project management software is also used for communication and collaboration between project stakeholders. Both free and paid versions of different project management software tools are available and some of the free project management software tools include: Learn More |
|
Virus Removal for AndroidAugust 07, 2018

Virus removal for android is one of the hot topics these days. Cyber attacks have evolved over the years, making them more invincible. To protect your Android smartphone from sophisticated cyber attacks, you need an antivirus app that offers the best virus removal tool for android. Learn More |
|
What is an MSP ? - A Brief DefinitionAugust 02, 2018

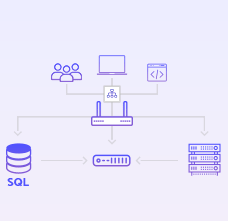
A managed service provider (MSP) offers a computing framework platform for the organizations to remotely manage their customer's IT infrastructure. The services may also extend to managing the end-user systems, basically on a proactive basis or under a subscription model. Learn More |
CLOUD BASED IT MANAGEMENT SOFTWARE FOR
MSPs and ENTERPRISE
Remote Monitoring and Management | Service Desk | Patch Management
Now Add Up To 50 Devices for Free